The Human-AI SOC
Connect disparate data sources to zero-in on the insights that matter to your organization and focus on threat prevention instead of reaction.
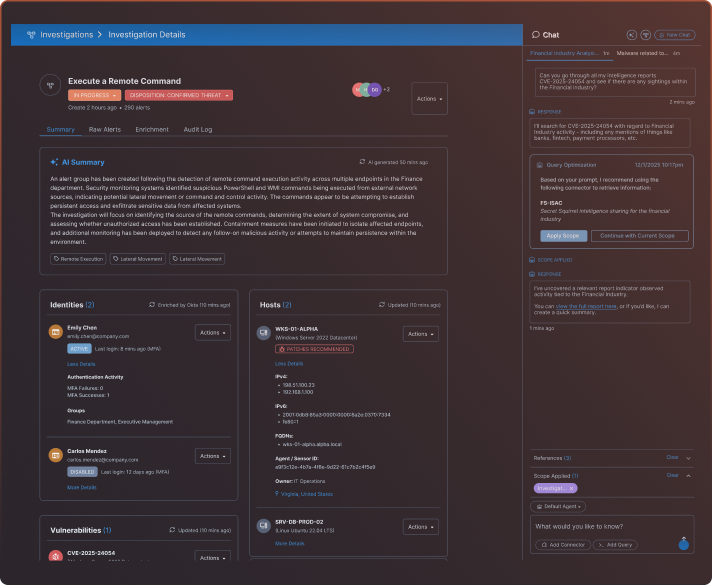
The Workspace for SOC Teams
- Prioritize alerts from multiple sources in a consolidated view.
- Automate investigation, high-volume alert management, and enrichment.
- Initiate investigation directly from the intelligence source, including urls and PDFs.
- Add multiple sources to the scope of a single investigation.
- Accelerate time to investigate and respond
- Collaborate to assess and determine risk levels.
Configurable
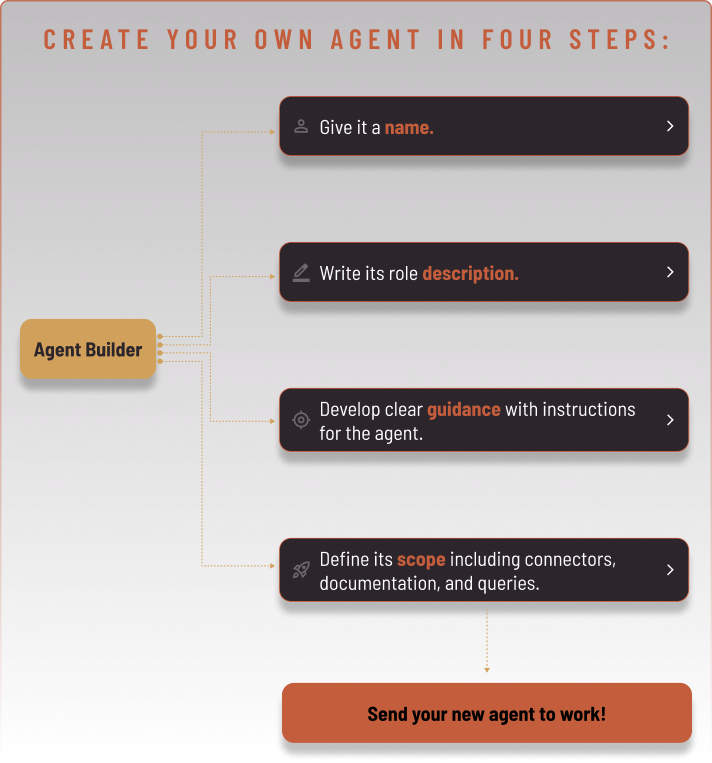
Agents
Configure your agents to focus on specific use cases, like phishing or alert triage. Or to support determined workflows or assignments, like looking for anomalies in the network.
Working under human oversight, the agents adapt to your ecosystem, enabling your SOC team to focus on the critical decisions, work smart, and build a sustainable advantage.
Estimate Your Outcomes
Safe AI Architecture™
Contextual
Awareness
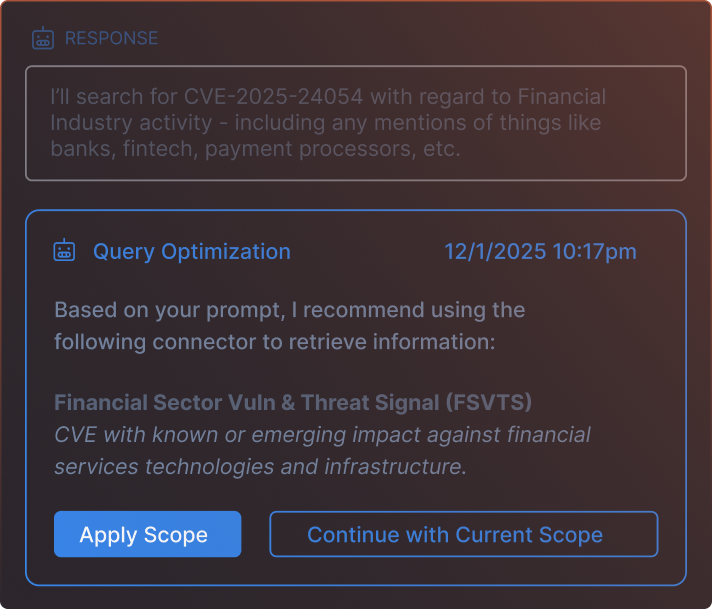
Get the actionable insights that matter to your organization’s specific risk profile.
No ETL Required
Enjoy less exposure, enhanced security, no migrations, and no delays.
Evidentiary AI™
Be audit-ready with AI-driven investigations that can be traced back to verified sources and insights.
Multiple Deployment Options
Choose the right deployment for your SOC — SaaS, air-gapped self-managed, or hybrid.
Use Cases

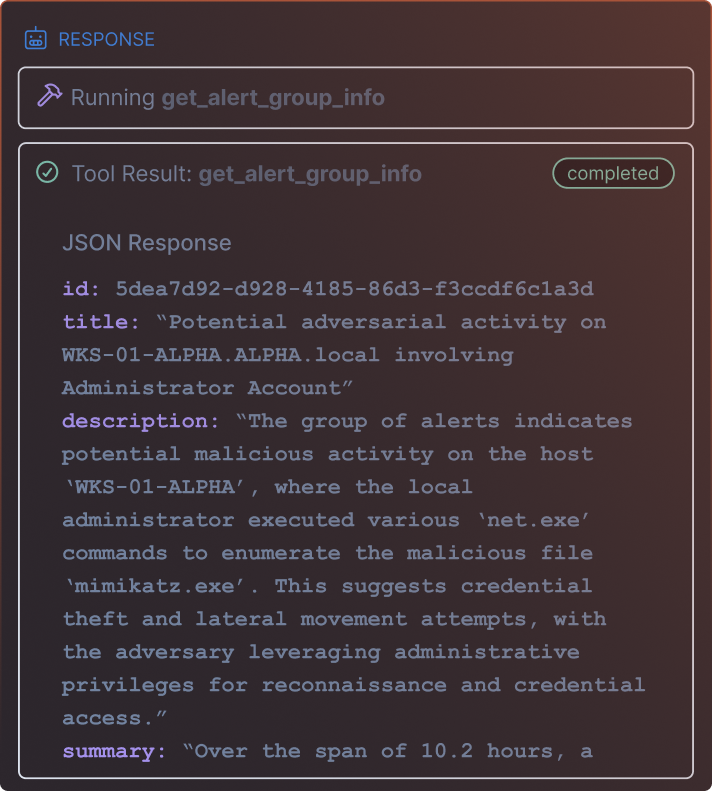
Alert Investigation
Investigate and prioritize alerts from multiple sources in a unified view, using AI-assisted context and enrichment playbooks to rapidly assess risk and drive confident decisions.

Cloud
Correlate and enrich cloud activity across logs and signals to quickly identify suspicious behavior and understand its context and impact.

Endpoint
Analyze and correlate endpoint activity to reconstruct timelines, assess scope and blast radius, and determine appropriate response actions.

Identity and Access
Detect and investigate identity-based threats such as credential misuse, anomalous access, and privilege abuse to quickly confirm risk and contain impact.

Network
Identify and investigate unusual network traffic patterns, including lateral movement and cross-signal activity, to uncover hidden or emerging threats.

Phishing
Swiftly identify phishing threats, investigate, and reduce attack risk.

Ransomware
Identify ransomware indicators early, assess potential impact, and support rapid containment to reduce operational and organizational risk.

Threat Hunting
Initiate investigations from analyst-driven entry points—including queries, documents, URLs, or alert groups—to proactively uncover threats and determine scope.

Threat Intelligence
Turn threat intelligence into action by launching investigations directly from intel sources (e.g., URLs, PDFs), enriching findings, and determining threat relevance and impact in minutes.