Andesite to deploy its Human-AI SOC to government agencies for mission-critical cyber defense
MCLEAN, Va., March 31, 2026 /PRNewswire/ — Andesite, the Human-AI SOC company, today announced that it has achieved Federal Risk and Authorization Management Program (FedRAMP) Authorized status at the High Impact Level. This milestone clears the path for federal civilian agencies to deploy Andesite’s Human-AI SOC to strengthen their cyber defense operations.
FedRAMP High Authorized requires a comprehensive assessment by an accredited third-party organization and formal authorization from a sponsoring federal agency. The designation signals that Andesite’s product, processes, and Safe AI Architecture™ meet the stringent security and risk management requirements demanded by the most sensitive government environments.
“Andesite is honored to achieve FedRAMP High Authorized, a milestone that reflects our deep commitment to protecting those who protect others,” said William MacMillan, Chief Product Officer at Andesite. “Government SOC teams face the same relentless flood of alerts and siloed tools as their enterprise counterparts, often with fewer resources and higher stakes. With full authorization in hand, we can now bring Andesite’s Human-AI SOC directly to those teams, empowering them to accelerate investigations, eliminate blind spots, and focus their expertise where it matters most.”
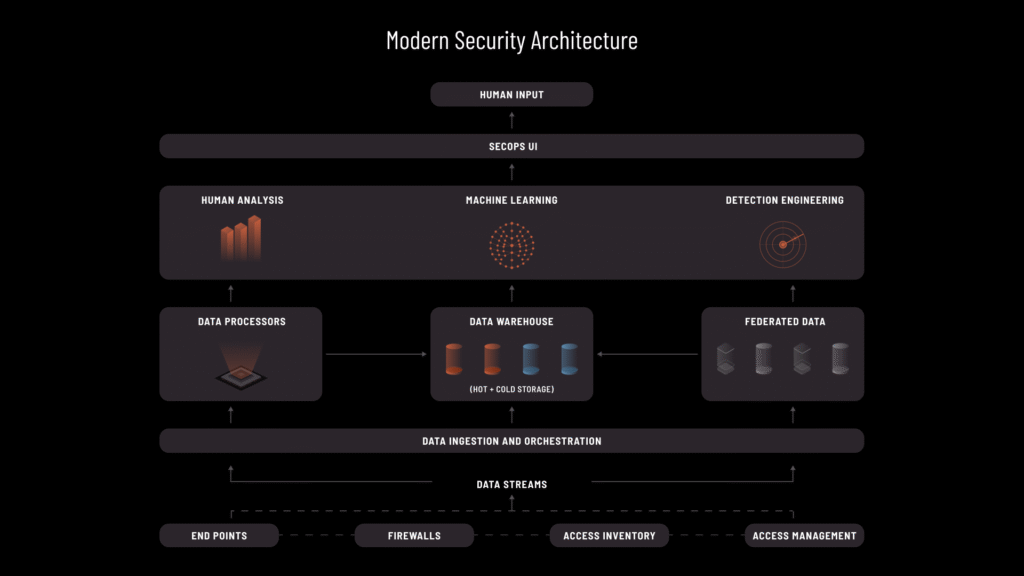
Andesite’s Human-AI SOC is purpose-built to automate triage, enrichment, and investigation while keeping humans at the helm of every critical decision. For federal agencies managing high-volume, increasingly sophisticated threats, the platform delivers contextual insights tailored to each organization’s risk profile, accelerates time-to-detect and response, and frees senior analysts to focus on prevention and threat hunting.
Andesite is secure and compliant by design. From inception, the company has built a security, trust and safety program that permeates all of its practices. Security is at the core of Andesite’s Human-AI SOC product. Their Safe AI Architecture™ protects customers’ data, applications, and networks with end-to-end encryption, no extract, transform, and load (ETL) requirements, and assurance that their AI is not trained on customers’ data.
FedRAMP High Authorized builds on a comprehensive compliance portfolio that includes SOC 2 Type II, NIST 800-53 (High), NIST CSF, ISO 27001, ISO 27701, ISO 42001, PCI DSS, HIPAA, CSA STAR, CSA AI-STAR Level 2, and HITRUST. Andesite’s Compliance High Trust Center documents over 500 continuous monitoring controls.
To learn more about Andesite and schedule a demo, visit andesite.ai.
About Andesite
Andesite puts humans at the helm, empowering SOC teams to build their own agents and oversee AI-driven automations. With Andesite, cyber defenders can automate triage, enrichment, and investigations to deliver detection and response at machine speed, while supervising evidence validation and making the critical decisions they are accountable for. Andesite arms organizations with safe defender AI that reduces attack surfaces and eliminates blind spots, powering the switch from a reactive to a proactive security posture before it’s too late to catch up with threats at scale. The company leaders and founders spent decades protecting our nation and some of the largest enterprises on the planet against sophisticated adversaries. Andesite embodies their sense of mission and commitment to develop security products that empower those who work protecting others. Visit us at andesite.ai, check our trust center at ComplianceHigh.com, and follow us on LinkedIn.
Media Contact:
[email protected]